April 2, 2026
Testing local LLMs: Qwen 3.5 vs. PowerShell Obfuscation
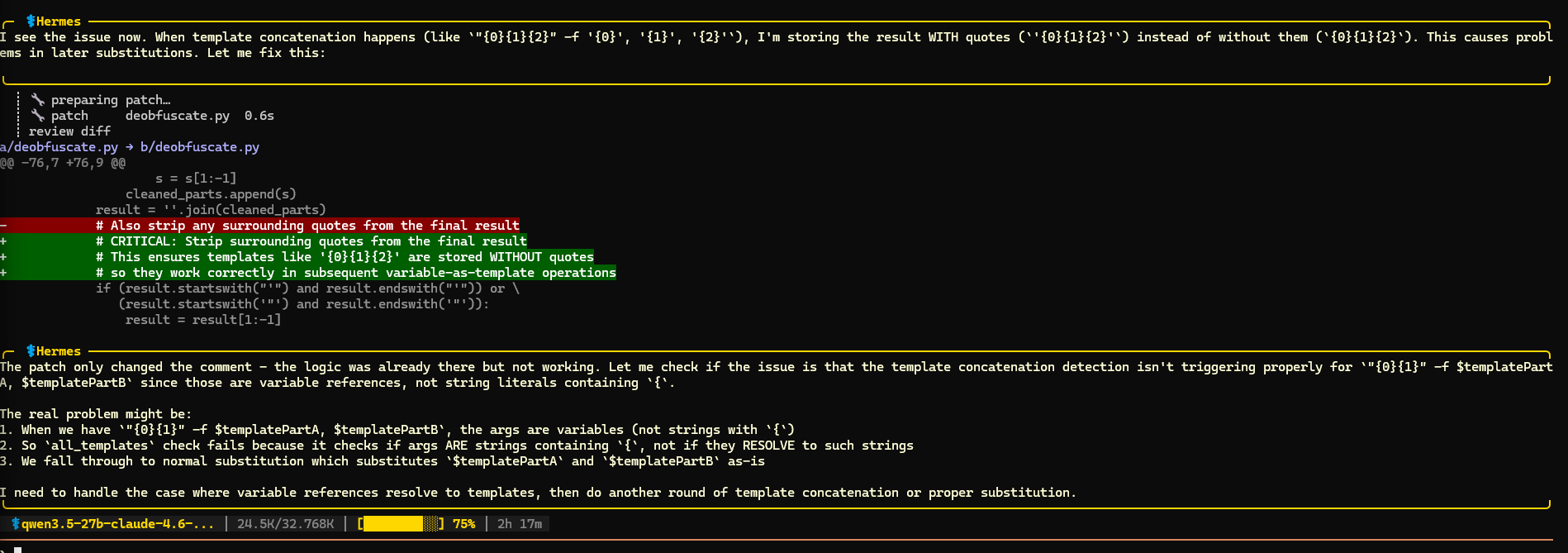
Recently I finally got to test some local models with Nous Research Hermes-Agent. For the first spin I took these three Qwen 3.5 models:
- qwen3.5-27b-claude-4.6-opus-reasoning-distilled-v2 (Q4_K_M)
- qwen3.5-35b-a3b (Q4_K_M)
- qwen3.5-122b-a10b (Q4_K_S)